I've had to find out whether an externally Linux library is installed on AIX system and whether something is not using it.
The returned errors was like so:
# gpg –export -a
Could not load program gpg:
Dependent module /opt/custom/lib/libreadline.a(libreadline.so.7) could not be loaded.
Member libreadline.so.7 is not found in archive
After a bit of investigation, I found that gpg was failing cause it linked to older version of libreadline.so.6, the workaround was to just substitute the newer version of libreadline.so.7 over the original installed one.
Thus I had a plan to first find out whether this libreadline.a is loaded and recognized by AIX UNIX first and second find out whether some of the running processes is not using that library.
I've come across this interesting IBM official documenation that describes pretty good insights on how to determine whether a shared library is currently loaded on the system. which mentions the genkld command that is doing
exactly what I needed.
In short:
genkld – creates a list that is printed to the console that shows all loaded shared libraries
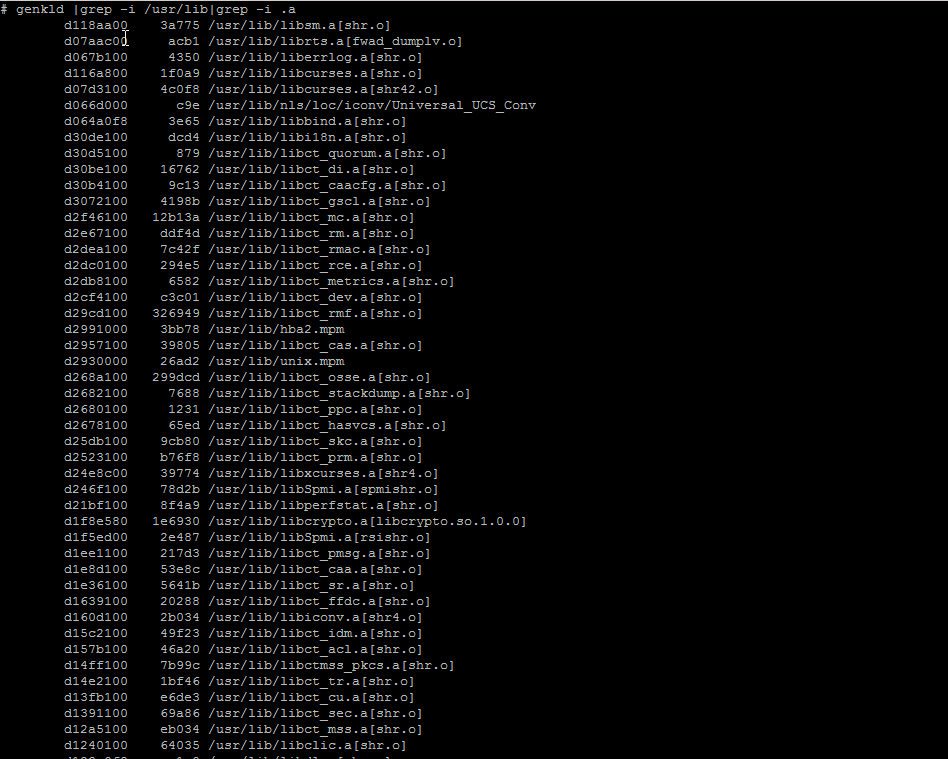
Next I used lsof (list open files) command to check whether there is in real time opened libraries by any of the running programs on the system.
After not finding anything and was sure the library is neither loaded as a system library in AIX nor it is used by any of the currently running AIX processes, I was sure I could proceed to safely overwrite libreadline.a (libreadline.so.6) with libreadline.a with (libreadline.so.7).
The result of that is again a normally running gpg as ldd command shows the binary is again normally linked to its dependend system libraries.
aix# ldd /usr/bin/gpg
/usr/bin/gpg needs:
/usr/lib/threads/libc.a(shr.o)
/usr/lib/libpthreads.a(shr_comm.o)
/usr/lib/libpthreads.a(shr_xpg5.o)
/opt/freeware/lib/libintl.a(libintl.so.1)
/opt/freeware/lib/libreadline.a(libreadline.so.7)
/opt/freeware/lib/libiconv.a(libiconv.so.2)
/opt/freeware/lib/libz.a(libz.so.1)
/opt/freeware/lib/libbz2.a(libbz2.so.1)
/unix
/usr/lib/libcrypt.a(shr.o)
/opt/freeware/lib/libiconv.a(shr4.o)
/usr/lib/libcurses.a(shr42.o)
# gpg –version
gpg (GnuPG) 1.4.22
Copyright (C) 2015 Free Software Foundation, Inc.
License GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html>
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law.
Home: ~/.gnupg
Supported algorithms:
Pubkey: RSA, RSA-E, RSA-S, ELG-E, DSA
Cipher: IDEA, 3DES, CAST5, BLOWFISH, AES, AES192, AES256, TWOFISH,
CAMELLIA128, CAMELLIA192, CAMELLIA256
Hash: MD5, SHA1, RIPEMD160, SHA256, SHA384, SHA512, SHA224
Compression: Uncompressed, ZIP, ZLIB, BZIP2