There is a quite a buzz online recently about the implications breach of personal privacy by simple browing online.
A week ago I've blogged On How to improve your web browser security for better personal identity
Though there is probably a plenty of more things to be done on guaranteeing your anonymous identity online, the article lacked to mention one very one vital project related with anonymity – the tor Anonymity online project
The project offer the user the right to be anonymous online through a complex constantly expanding network of volunteers which voluntary install and grant access to the installed tor server to be used as a proxy from their computers.
A very thorough explanation on what is tor can be red here
Enabling tor on your personal computer would at least guarantee you that every now and then your traffic browser network traffic (request) would flow through a random tor servers located on a different worldly geographic locations.
Usually the traffic to a destination host would pass through 5 tor network nodes. Where the traffic is unecrypted between last node and the 4th node, while in the other four ones it's completely crypted.
This makes your tracking almost impossible if it's based on technologies like for instance Maxmind's Geoip or Geonames's geographical data base because every now and then you'll appear to be coming to the end point referrar web server originating from a different tor node ip address
The tor server is a free software licensed under the GPL and this is also a good assurance because everybody is able to have a look on the code and this is a further guarantee that the software doesn't include a malicious ways for a middle users to sniff on your traffic.
The tor project has even built a pre-bundled browser ready to be worn by yourself on a usb stick, so you can quickly start using the tor anonymous network on any random computer anywhere.
The tor browser page is available here also Tor Browser Bundle for Windows is available here
Tor server is available for both Windows, Mac OS X, Linux and Linux/BSD Unix
Of course tor is not perfect it opens some other possible doors for attackers which are much less likely to occur if you don't use it, however in general it's better off with tor than without it.
One serious reason for not reason for not using Tor might be that it's usually many times slower than normal browser since, it routes traffic through a different tor network nodes.
So if you decide to go on and use it you better be patient and calm 🙂
Since I'm a Debian user and I really do value my privacy I decided to start using Tor.
In order to start using Tor it's usually necessary to configure your browser to use The TorButoon Firefox browserextension
Nevertheless on Debian GNU/Linux if you try to go the straigh way as explained on Tor's website install the TorButton and configure it to work in cooperation with the polipo caching proxy
You will be not able to browse after enabling straight the tor plugin.
If you try the up-mentioned approach you're probably about to come to errors like:
"the proxy server is refusing connections"
,
Proxy error: 502 Disconnected operation and object not in cache
or
504 Connect to superquizgames.com:80 failed: SOCKS error: host unreachableThe following error occurred while trying to access http://yourwebsite.com/:504 Connect to superquizgames.com:80 failed: SOCKS error: host unreachable
In order to properly install configure and enable the TorButton on my Debian GNU/Linux I had to get through the following steps:
1. Install the polipo caching proxy
debian:~# apt-get install polipo
2. Download and overwrite default polipo configuration with the one from torproject.org
This is necessary to configure in order to have polipo adapted to work with tor, so issue the following commands:
debian:~# cd /etc/polipo
debian:~# wget https://svn.torproject.org/svn/torbrowser/trunk/build-scripts/config/polipo.conf
debian:~# mv config config.bak
debian:~# mv polipo.conf config
3. Restart polipo for the new config settings to take affect
debian:~# /etc/init.d/polipo restart
4. Install the iceweasel-torbutton browser extension
debian:~# apt-get install iceweasel-torbutton
The iceweasel-torbutton will also install you the tor package which is evidently required for the torbutton to operate.
Now you should be ready to go, you can enable the tor use from the tor button which should appear in your browser in the bottom right corner of your browser.
It should look something similar to:
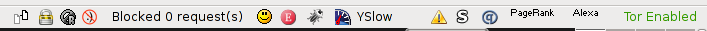
Tor Enable/Disable Iceweasel browser Button
To test your Tor Configuration you can use the Test Settings button which is straight available from TorButton's preferences
From here after it might be a good idea to play with the TorButton security settings and configure it according to your liking, bear in mind that you should have a solid knowledge on how browsers work and some basic Internet protocols before you start tampering this options.
If tou don't know what you do you better stop and don't tamper with the torbutton security options.
The only one that you will most probably want to untick is The Disable plugins during Tor usage , stopping this option will allow you to have a flash video streaming display properly, otherwise you won't be able to use , Vbox etc.
Below you see a screenshot of the TorButton Security Settings dialog.
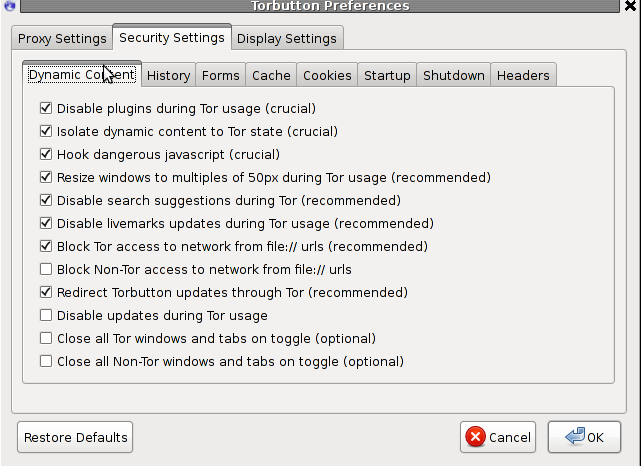
To open up this dialog you need to navigate to the TorButto and choose preferences with the right mouse buttons 🙂
Hope this article is informative to somebody out there.
User feedback is mostly welcome! Cheers 🙂
More helpful Articles

Tags: Button, configure, How to, How to install and configure torbutton on Debian / Anonymizing Iceweasel on Debian GNU/Linux, Install, mouse, network traffic, polipo, Restart, servers, unreachable, web browser security








Mozilla/5.0 (Windows; U; Windows NT 5.1; pl; rv:1.9.1.3) Gecko/20090824 Firefox/3.5.3
Very good.
View CommentView CommentMozilla/5.0 (X11; U; Linux i686; en-US; rv:1.9.1.16) Gecko/20110302 Iceweasel/3.5.16 (like Firefox/3.5.16)
sudo mv -i /etc/polipo/config{,.dpkg-dist}
sudo wget -O /etc/polipo/config https://gitweb.torproject.org/torbrowser.git/blob_plain/HEAD:/build-scripts/config/polipo.conf
sudo service polipo force-reload
View CommentView CommentMozilla/5.0 (X11; U; Linux i686; en-US; rv:1.9.2.17) Gecko/20110422 Ubuntu/10.10 (maverick) Firefox/3.6.17
This didnt work for me it gave me a 404 when i tried https://svn.torproject.org/svn/torbrowser/trunk/build-scripts/config
View CommentView Commentsomeone please help me.
also when i manualy try to change the config file i couldnt find it.
can anyone tell me where it might be located please thanks.
Mozilla/5.0 (X11; U; Linux x86_64; en-us) AppleWebKit/531.2+ (KHTML, like Gecko) Version/5.0 Safari/531.2+ Debian/squeeze (2.30.6-1) Epiphany/2.30.6
Hi Dante,
Here is a copy of the polipo.conf I use mirrored:
http://www.pc-freak.net/files/polipo.conf
Use this one and it should be fine.
Drop me a message if it is fine with this conf and I will fix the url as well in the article.
Best,
View CommentView CommentGeorgi
Mozilla/5.0 (X11; Linux x86_64; rv:52.0) Gecko/20100101 Firefox/52.0
Unfortunately torbutton is no longer working on Debian GNU / Linux. Instead the only option is to use tor browser bundle.
View CommentView Comment