Yesterday I drinked 200 gr. of Vodka yesterday Night, it was pretty refreshing for me but I got drunk a little.I'm smoking again … Things are going bad in my life recently. I have health issues. And I intend to go to doctor today.Yesterday I went to the polyclinic but my personal Dr. Nikolay was not there (I was angry, I went to doctor once in years and he is not there) so I'll try again today. I had pains somewhere around the stomach. At least at work things are going smoothly at least God hears my prayers about this. I'm very confused and I have completely no idea what to do with my life. Yesterday I was out with Lily and Kiril on the fountain. The previous day Nomen, I, Yavor, Kiro and Bino went to the "Kobaklyka" (a woody place which is close to Dobrich.) Well that's most of what's happening lately with my life. I wrote a little script to make that nautilus to get restarted if it starts burning the cpu. It's a dumb script (the bad thing is that I'm loosing form scripting, Well I don't script much lately). Here is the script http://pcfreak.d-bg.net/bshscr/restart_nautilus.sh https://www.pc-freak.net/bshscr/restart_nautilus.sh. The days before the 4 days weekend, I hat to spend a lot of time on one of the servers fighting with Spammers. Hate spammers really! I ended removing bounce messages at all for one of the domains, which fixed the bounce spam method spammers use (btw qmail's chkuser seems to not work properly for some reason) … Also I started watching Stargate – SG1. First I thought it's a stupid sci-fi serial. But after the first serie I now think it has it's good moments :]. Also I had something like a Mortification Day going on during Monday. The whole day I listened to Mortification (The first Christian Death Metal Band). I Liked much the "Hammer of God" album. In the evening Sabin (Bino) came home and we watched some Mortification videos at Youtube. Right now I listen again to "Ever – Idyll" a pretty great song. And yeah I keep listening to ChristianIndustrial.net a lot, a great radio. Try it if you haven't!END—–
Posts Tagged ‘Spammers’
Xtractor Extreme, Power Email Harvester and AMS (Advanced Mass Sender) three Windows programs to Beware of
Monday, August 15th, 2011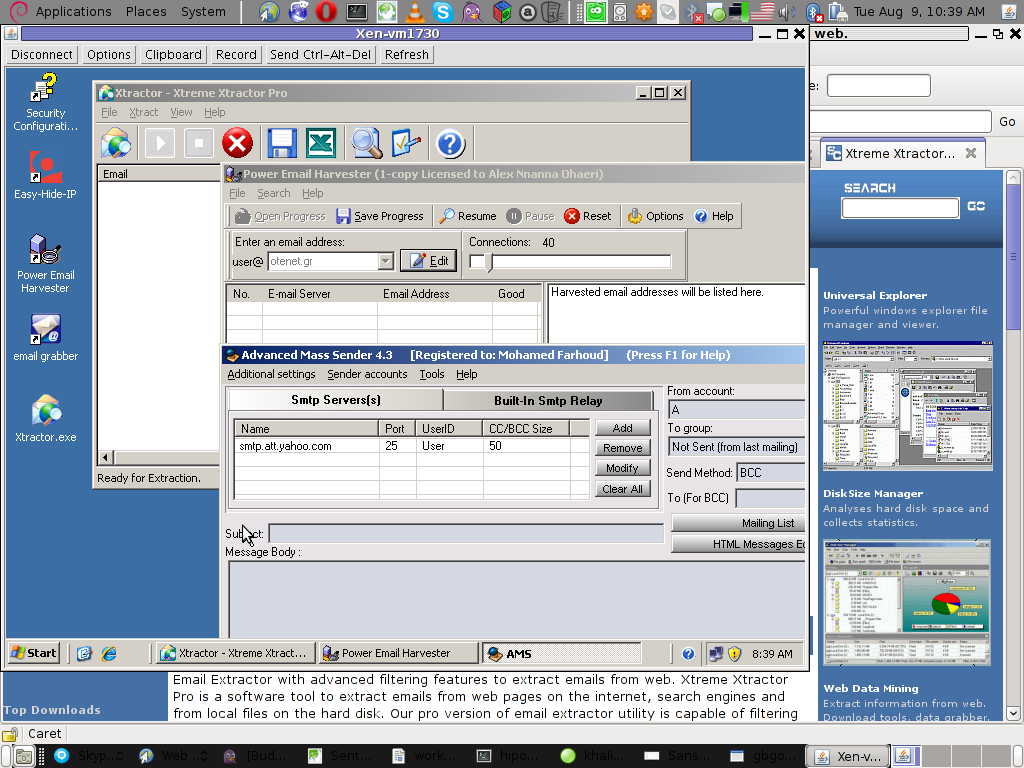
Few days ago, I’ve catch some Spammers on some of the servers running Windows inside Virtual Private Servers.
I was doubting if I want to write an article to mention about this 3 piece of software as it might be a bit boury however eventually I thought the goods of it will be better so I just took minutes and wrote it.
Back to the topic the three programs which the spammer was installed and prepare to do his spamming job on the VPS server was:
1. Xtractor Extreme
2. Power Email Harvester
3. Advanced Mass Sender
In order to hide his real IP address and prevent the IP he was spamming, he has also installed some anonyous proxy like Windows software called Hide My IP
The first program Xtractor is basicly an Email collector, the program crawls the net and searches to match email string on web pages.
It get target websites from major search engines.
You put an email like @gmail.com inside it and it starts spidering and grabs all email strings under the domain @gmail.com. Besides that Xtractor Extreme Pro is freeware and can be easily downloaded from many locations online.
Power Email Harvester‘s program name is also quite self-explanatory, what it does is it digs the net for email addresses and generates spam lists … This is the ultimate tool for a spammer, however the guys who create this piece of disruptive software has branded it as “a marketing tool” and even sold and advertised as a tool to help an e-marketing campaign.
This is of course just a word play and in fact in my viewe these program should be prohibited by international law.
Advanced Mass Sender is another piece of Spammer software which officially is tagged as marketing software and is sold and recommended as an useful tool for e-marketing.
I’ve take the time to take a quick and test the spammer installed AMS , honestly I’ve been amazed how far spamming has went during the last 5 years.
This AMS shit is capable of creating a target groups which could easily be spammed whether each group can contain up to 200000+ ! target emails
Advanced Mass Sender can even check if a certain email is present on the remote mail server and only then tries to deliver.
Besides that it even supports sending the spam mails via multiple mail servers (simultaneously) to increase the thoroughput as well as supports proxy servers…
I decided to write this few lines article to raise some awareness about this shitty sofware in a hope that somebody who is Administrating / Supporting client owned Windows servers or Virtual Private Servers will be able to read about this 3 ones and stop spammers before they succeed to create mail havoc with their ugly spam stuff.





