Those who remember the times of IRC chatting long nights and the need to be c00l guy and enter favorite IRC server through a really bizarre hostname, you should certainly remember the usefulness of Reverse SSH Tunnels to appear in IRC /whois like connecting from a remote host (mask yourself) from other IRC guys where are you physically.
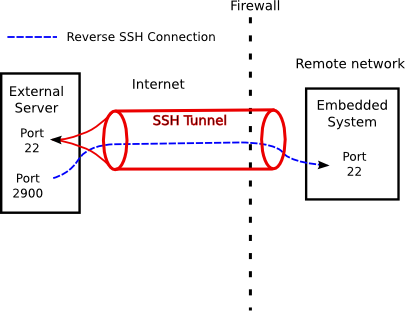
The idea of Reverse SSH is to be able to SSH (or other protocols) connect to IPs that are situated behind a NAT server/s.
Creating SSH Reverse Tunnel is an easy task and up to 2 simple SSH commands,
To better explain how SSH tunnel is achieved, here is a scenario:
A. Linux host behind NAT IP: 192.168.10.70 (Destination host)
B. (Source Host) of Machine with External Public Internet IP 83.228.93.76 through which SSH Tunnel will be established to 192.168.10.70.
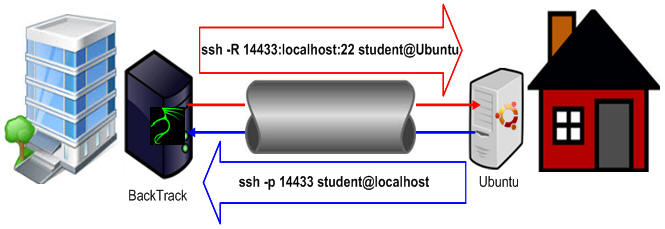
1. Create SSH Revere SSH from Destination to Source host (with Public IP)
Connect to the remote machine which has a real IP address and make port of the reverse SSH connection open (remove any firewall), lets say port 23000.
ssh -R 23000:127.0.0.1:22 username@DOMAIN.com -oPort=33
NB! On destination and source servers make sure you have enabled in /etc/ssh/sshd_config
AllowAgentForwarding yes
AllowTCPForwarding yes
PermitTunnel yes
2. Connect from Source IP to Destination through the established SSH tunnelling
Connecting to DOMAIN.com through ssh on 23000 will connect you to the back machine with the unreal IP address.
ssh local-username@127.0.0.1 -p 23000
ssh -L 19999:localhost:19999 middleman@178.78.78.78
If you want other server with hostname whatever-host.com to access the Reverse SSH Tunneled server you can do it via external IP which in my case is 83.228.93.76
From whatever-host.com just do:
ssh username@82.228.93.76
A text diagram of SSH Tunnel looks something like that:
Destination (192.168.10.70) <- |NAT| <- Source (83.228.93.76) <- whatever-host.com
Above examples should work not only on Linux but on NetBSD / OpenBSD / FreeBSD or any other UNIX system with a modern SSH client installed.
More helpful Articles

Tags: create ssh tunnel, reverse tunnel ssh, ssh







