A friend of mine gave me an interesting link it’s about Pravetz A computer systems which were an absolute hit here in Bulgaria, they are produced here and we should be proud we had our Bulgarian computers. Here is the link Pravetz! 🙂

Pravetz was a was copy of Apple ][ (Pravetz 8A, 8C, 8M), Oric (Pravets 8D) and IBM-PC (Pravetz 16 also known as XT).
Pravetz was named after a town of Pravetz which is the homeplace of the ex-Bulgarian communist party leader and President of Socialist Bulgaria Todor Jivkov. Pravetz had a huge production quantities as about 200 000 were exported to coutnries from Soviet Union block. My generation people about 30 have grown with Pravetz and many nowadays IT specialists in Bulgaria had learned computer basics on 8 or 16 bit Pravetz machine. Its compatability with DOS made it a great game-station PC. Owning Pravetz PC at communist times was considered as a sign of elitism as only Police station and highest authorities or people close to party leaders had one of those even in 1995 still owning a Pravetz PC was considered an extra-ordinary think.
Pravetz 16 was part of the MIK-16 family of computers, which included:
– Pravetz 16 (the one on the picture, 4.77Mhz)
– Pravetz 16A (1x Floppy, 1x 5MB HDD)
– Pravetz 16H (improved one, 8Mhz, 1 or 2 Half size floppies + 1x HDD 20MB – half size)
– Pravetz-286
The first version of Pravetz 16 had a built-in Basic on a ROM chip, which loaded if no OS was present. The 16A did not have a built-in Basic.
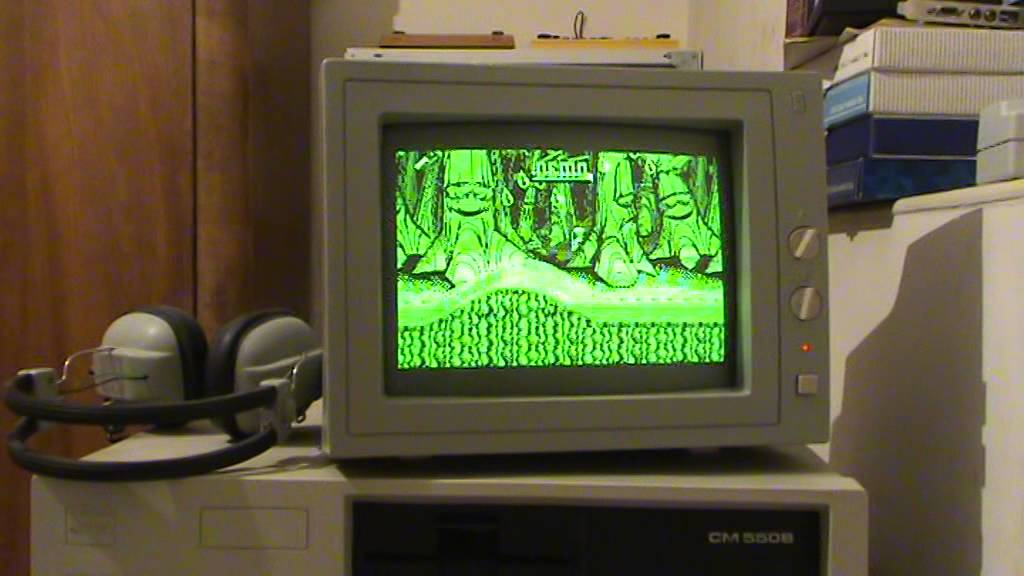
The 20 Megabytes HDD was a revolution, for almost 4 years the HDD never show any errors. There was a CGA (Color Graphics Adapter) built-in control, and i had a 16-color display (or monochrome black and green display based on the model). This machine was excellent for making DOS-programing, and was used till the middle of the 90’s, mostly in government facilities.
The following software was available for Pravetz:
-programing languages (BASIC-16, PASCAL, Cobol,Ada);
-dBASE systems (Micro-PC-2);
-Text editors (Text-16, MicroTEXT-16, DOKS-2);
-Electronic schedules (Superplan-16, MicroPLAN/16);
-information-searching systems (INFOS);
-Administration automatisation (MIS);
-Integrated products (MULTIPACK);
-Machine graphics;
-CAD (GraphCAD, PLOT-1);
-communication utilities;
-learning&enjoy programs;
-specialised products.
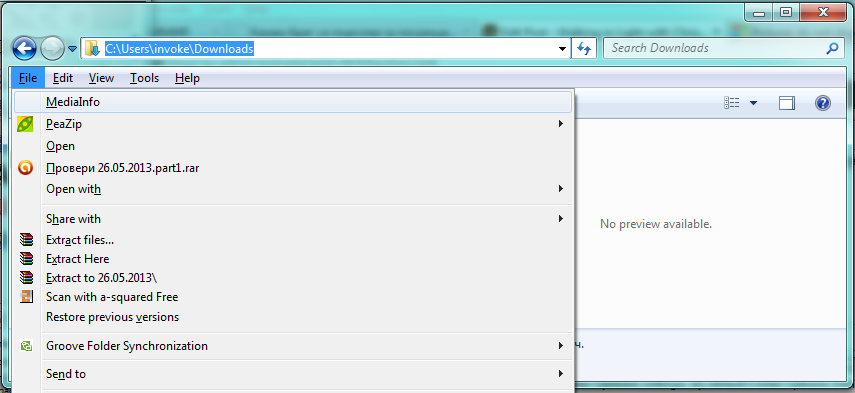
Many people were installing MS-DOS 5.0 or 7.0 or DR-DOS and using the PC with DOS programs, where most compatible with XT were working just fine. My own monitor was monochrome and had problems with displaying some color gammas and thus in Games some of the colors were not displayed. However owning a Pravetz was amazing thing at that time, it was a mania and a building block of a whole PC-geek generation that emerged from Pravetz Culture.
At that time in the distant 1988 when Bulgaria was still highly industrialized country in Plovdiv we were producing another made in Bulgarian Computer called Puldin (Puldin is the ancient name of the city of Plovdiv Bulgaria).
What was unique about Puldin was it was computer completely built from scratch with its own hardware and software architecture.
Puldin was produced in 4 modifications 601-A/U/M/T, the RAM memory was 64KB, the ROM was from 4KB up to 68KB depend on the model, the video output could be connected to normal TV, there was LAN card, Printer centronics output, Cassete input, RS232, Floppy disk, etc.

As you can see in above screenshot the keyboard was slightly different from Pravetz one it gives an impression of unique design (Apple Mac styled) 🙂
Though keyboard looks nice it was terrible to use, there was no tactile click feed back so you basically don’t know if you pressed the key, fortunately later models had connector for external IBM-PC keyboard with keys, which make the work easier.The computer was already unefficient as in 1988 there were already lot of computers on the market including IBM-PC with 16 bit processor running at the remarkable 4.77Mhz.
Puldin processor was a Motorola 6800 copies named CM601 at that time produced in Botevgrad. It was running UniDOS which was basically a made from scratch MS-DOS alternative.
The computer was equipped with Assembler, BASIC, Pascal, Editor, Diagnostic tools, even DBase equivalent. Puldin was produced in small volume ~ 30 000 – 50000 computers mainly shipped to Russia as Russia was main market for Bulgarian products at that time. Software developed on Puldin could be moved to IBM-PC by using Pascal P-code and this was highly revolutionary as it had capabilities similar to Java long before Java was existent.
Computer was developed by 6 developers which were students at that time and they made it as enthusiasts without taking a penny for it. One of the software developers who worked on Puldin was also author of Eagle DOS for Apple ][ (Pravetz82) and UniDOS for Puldin and now has his own company selling computers http://eagle.bg.
The guy who wrote the Assembler BIOS and Basic ROM for Puldin – Todor Todorov became more famous with his virus works instead of what he did for Puldin the now mythological Dark Avanger