Some few months ago, I’ve posted some study materials for e-marketing & commerce course (discipline) that I followed in Arnhem Business School (ABS)
Apart from that I had a final assignment which was supposed to be handed in some few weeks before the begging of the Christmas break.
The Emarketing assignment’s aim was to make a comparison of two websites which are operating in the same or very similar business field
The report’s goal was to present to the E-marketing teacher which in my case was Peter Stemers that the student has been acquainted with the basic theories of Emarketing.
The project was actually rather easy and the main issue to build up a project like this is the start up to complete it you just need to put a start and persist in expanding the document.
As the topic was very interesting to myself I started quite early in preparing my assignment (just a few weeks after it was assigned).
I’ve considered my profound interest into Information and Computer Technology (ICT) and decided to create a report which evaluates two websites which are into the IT sphere.
After a examination over a few possible domain names like for example:
Verizon – verizon.com and AT&T – att.com
1& 1and1.co.uk and Godaddy etc.
I’ve finally set my websites to compare choice on: Godaddy.com and enom.com
The criterias for selection of Godaddy and Enom as a target companies to compare their online business was as follows::
1. Both Godaddy and Enom are into the same business online industry, ( e.g. domain selling, reselling, blog hosting, webhosting, SSL certificates, online presence Search Engine optimization etc.)
Some other selection factor that convinced me to choose exactly Enom.com and Godaddy were that this are the biggest companies in the domain names selling IT sector and even better the Domain Selling industry has a tight relation to the History of how the Internet emerged.
The report became really thoroughful, the Godaddy vs Enom emarketing report has the size of 59 pages. Officially the study criterias has been that normally the usual student emarketing reports contains about 15 to 20 pages, however as the business products and services that this huge internet domain reseller companies has, I was forced to exceed the set teacher limitation of 20 pages and do it in 59 pages.
I’ve handed in my emarketing report and Peter Stemers graded it with 8.5 points from 10 possible (which by the way is quite a high mark for Arnhem Business School)
By the wat the E-marketing course was quite a silly one though for people that are not have an avarage computer knowledge and interest into Internet Commerce it was okay.
To read the table of contents of the Report comparison Enom compared to Godaddy click over here
Here is also my Emarketing Final Report Godaddy.com vs Enom.com (Godaddy.com compared to Enom.com) in both PDF and DOC, I hope this reports will be helpful to some marketing researchers out there to get an estimate on how the two companies are performing in the domain selling and reselling business:
2. Download E-marketing report Godaddy.Com VS Enom.Com (Godaddy.com Compared to Enom.com) in PDF
Compiling this Emarketing report costed me a lot of effort and time, the overall completion of the report has took me about a two weeks time, whether each day I worked a couple of hours on it.
I express also my big thanks to Alex Petrov (a friend of mine) for helping me read and review the report and fix some minor errors in sentence structures and my language of expression.
The Godaddy VS Enom Emarketing report outlines, numerous pitfalls that both Enom Company and Go Daddy has done in terms of SEO, Emarketing, user friendliness and usability
I believe this report could be really helpful for the these two competitive companies and could help them improve both their user image, their accessibility and Search Engine indexing.
On the other hand the report could be a good example for (HAN – Arnhem Business School E-Marketing) students on how to write a good looking Emarketing report to give themselves a pass.
An interesting fact is that before I decide to publish the report online and make it available to everyone I tried a known selling marketing report, I tried to offer to both Godaddy.Com and Enom.Com to sell them this report by sending the offer to their marketing and sales guys.
Enom.com has returned me an email, that they will look forward to my request, whether with Godaddy I have received an email by Go Daddy founder and CEO Bob Parons and the COO Warren Adelman
I will present you here the reply just to show you how impodent this mans are! My offer to sell them this great report for the symbolic sum of 200 EUR which will help their companies grow was considered I quote: “Unsolicated Report”.
Below I present you my offer email plus the impudent reply email by GoDaddy’s CEO and CEO:
SNAP – My Email to Godaddy
Hi Bob,
My name is Georgi Georgiev and I’m currently completing my bachelor in
Business Administration in HAN University of Applied Sciences (The
Netherlands).
Currently I’m developing an E-marketing report which is comparing the 2
largest internet domian registrars
godaddy.com and enom.com.
The report is a in depth SEO and E-marketing analysis of current
positioning in major search engines of Godaddy.com and Enom.com as well
as an overall analysis of user user friendliness, screen resolution
readiness of the two websites.
In the report I also analyse the behaviour of the enom.com and
godaddy.com as tested with different major Internet web browsers,
general user experience. External statistical websites etc. etc.
This research document does also concludes what are the strengths &
weaknesses of both your company and enom.com. The aim of the report is
to show, what Godaddy advantages and pitfalls if compared to Enom.com.
It also includes a number of suggestion for improvements which will be
beneficial for your company to drive more internet traffic to you as
well as increase your number of customers.
The report is 60 pages long document and includes many things that might
be beneficial for your business.
If you’re interested into the report and you’d like to buy it for me for
a very cheap price of 200 EUR, please contact me on my mail
hipo@www.pc-freak.net or systemexec@gmail.com.
Best Regards,
Georgi
—
Georgi Georgiev
——
END of SNAP
SNAP – Godaddy’s Bob Parson and Warren Adelman Reply Email:
Office of the President Response
Dear Georgi Georgiev,
Thank you for contacting the Office of the President. Our CEO, Bob Parsons, and President and COO, Warren Adelman, have asked me to respond on their behalf.
We value your time and appreciate the information you have provided regarding this request. Please understand that we are not seeking to acquire any unsolicited reports of this nature at this time.
Thank you for your understanding.
Sincerely,
Jordan McAlister
Hope this post is helpful to some students stucked with writting their E-marketing report
I also hope it shows how proficient, I’m in building reports and might be a good exapmle on how qualitative my work is and enhearten somebody to hire me as an E-marketing consultant 😉










A must have collection of WordPress plugins that enpowers your blog and improves SEO
Tuesday, April 5th, 2011Since I’m using wordpress as a blogging platform for about two years now and I’m constantly experimenting with valueable wordpress plugins.
I’ve decided to publish a compilation of wordpress plugins that empowers my blog
The plugins included in the compilation are quite various, some of the plugins aims at easy post sharing via the general social networks and main websites used by users today, others significantly helps in increasing the blog ranking in major search engines, there are some that adds like button to the blog.
These plugins also strenghthen the easy blog RSS file sharing, some post straight to twitter all your blog posts, generate tags automatically, puts a better features to the default wordpress commenting mechanism, prevent from spam comments, add features for easily adding Google adsense to the wordpress installation to help you advertise on your blog.
There are also plugins which delete duplicate posts (if you have such), puts better wordpress blog search bar, generates a sitemap to the blog, add an option to include php codes straight into your posts, adds wordpress an option to easily put mod rewrite rules straight from the wordpress interface, boost wordpress speed by adding static html generation cache, boost performance etc. etc.
Here is the complete list of wordpress plugins which I have currently installed on my wordpress blog:
ad-squares-widgetadd-to-any-subscribe
advertising-manager
ajax-comments
akismet
all-in-one-adsense-and-ypn
all-in-one-seo-pack
askapache-google-404
auto-tag
bm-custom-login
commentluv
comments-statistics
cyr2lat-slugs
delete-duplicate-posts
easy-adsenser
extended-search-plugin
facebook-share-new
favourite-bible-verse
feedburner-plugin
feedburner-widget
feedburner_feedsmith_plugin_2.3
feedlist
force-publish-schedule
google-analytics-for-wordpress
google-sitemap-generator
headspace2
my-link-order
php-code-widget
platinum-seo-pack
post-plugin-library
post-to-twitter
profile-pic
profile-pics
redirection
rss-atom-avatar
seo-automatic-links
seo-slugs
share-on-facebook
share-this
similar-posts
simple-tags
subscribe-to-comments-reloaded
subscribe-to-comments
subscribe2
text-control
tidy-up
tinymce-advanced
what-would-seth-godin-do
wordbook
wordpress-23-related-posts-plugin
wordpress-mobile-edition
wordpress-thread-comment
wp-codebox
wp-keiths-easy-rss
wp-likes
wp-o-matic
wp-postviews
wp-super-cache
wp-syntax
yourls-wordpress-to-twitter
I do have enabled most of the plugins, though some are disabled but still might be helpful somewhere in the close-future thus I still keep them installed.
I would skip the time to describe one by one what each of the above list of plugins will do for your wordpress, since the list is quite long.
However I defnitely think this is a list of plugins you might want to have installed in a newly established wordpress blog for sure.
Note that the versions of the plugins which are included in this must have wordpress plugins collection might not be the latest as the included ones are the ones I do have installed at the time of writting of this article.
Also be aware that some of the plugins might create some issues with newer versions of wordpress (your blog might beak up!), however most of the plugins should work out of the box by just enabling each one of them from the wordpress interface via the menus:
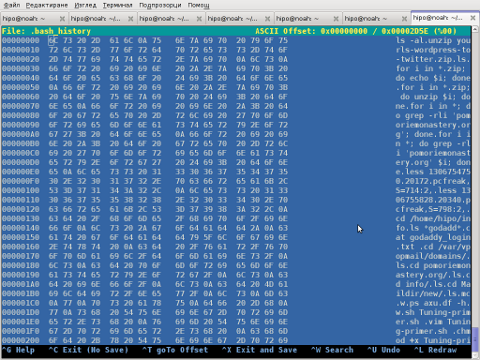
Settings -> Plugins -> InactiveTo straight install my bundled package of plugins you have to issue the commands:
linux:~# cd /var/www/blog/wp-content/pluginslinux:/var/www/blog/wp-content/plugins# wget https://www.pc-freak.net/files/a_must_have_wordpress_plugins_collection.tar.gz
linux:/var/www/blog/wp-content/plugins# tar -zxvf a_must_have_wordpress_plugins_collection.tar.gz
...
linux:/var/www/blog/wp-content/plugins# unzip *.zip
Now as they should be installed under the plugins directory go and enable the plugins.
Further on many of the plugins will require configuration from the menus:
Settingsor in the menu
Tools
After being setup up your new wordpress installation will look significantly better, you will notice a tons of useful features which you might have previously missing and desperately needed 😉
Most of the bundled package of wordpress plugins works fine with wordpress version 3.1, if you’re trying to install enable and configure the plugins on some other versions of wordpress, there might be problems!
If you experience problems by trying out my bunch of wordpress plugins please drop me a comment.
I hope you enjoyed this improvised article, if these bunch of plugins are useful to you please give me a thanks 🙂
Thanks!
Tags: adsense, advertising manager, aims, ajax, analytics, auto tag, bible, bible verse, blog, boost, Button, collection, commentluv, compilation, complete list, configure, custom login, cyr, drop, extended search, generation, google, google sitemap generator, html generation, Inactive, installation, interface, major search engines, mechanism, mod, option, package, php, platform, plugin, post, Search, search bar, search plugin, SEO, Settingsor, Slugs, social networks, squares, time, twitter, wget, widget, wordbook, Wordpress, wordpress blog, wordpress plugins, ypn
Posted in SEO, Web and CMS, Wordpress | 8 Comments »